Spying and the Fermi Paradox
By UAP Bridge
24 June 2021 22 minute read
Author’s note: This is the original, longer form article that was revised and shortened for The Great Strategic Silence. It was originally published on my old blog ETITheory, which I shut down and moved the content here to consolidate my work. You can see archived versions of Spying and the Fermi Paradox on ETITheory from June 2021 on Wayback Machine here and Archive.today here. The publication date of 24th June 2021 was the day before the release of the Pentagon’s UAP Report, as I was concerned that some of the below might be released in that report, so rushed to get it out in advance (but it was not).
“There is no place where espionage is not possible”
–Sun Tsu, around 500 BC [1]
1. Abstract
The Fermi Paradox asks: Given that commonplace assumptions suggest the galaxy should be teeming with intelligent life, why have we not detected any?
Meanwhile, a practically ubiquitous pattern in terrestrial international relations is covert intelligence – i.e. spying on others and keeping information hidden from them for strategic benefit. We seek to understand if such strategic intelligence incentives could explain the Fermi Paradox.
We break the question into two parts. First, considering game theory and the terrestrial history of spying, we ask we ask to what extent ETI in general would be incentivised to covertly spy on human-level civilisations. Second, we conduct a thought experiment: If ETI were spying on Earth, what would the evidence look like, and is it likely the scientific community would be aware of it?
We find that there are significant and universal incentives to support ETI spying on human-level civilisations for simple, strategic intelligence reasons. We therefore propose this as a solution to the Fermi Paradox. Our analysis suggests ETI spying would likely show predictable patterns of evidence, and that some of this evidence would likely have been detected. But we find that it is unlikely the scientific community in general would be aware, partly due to assumptions of the scientific method causing false negatives with this type of non-reproducible, intentionally deceptive evidence. Finally, we propose how our predictions could be tested.
2. Introduction
What is the Fermi Paradox?
The Fermi Paradox is simply stated: Current observations suggest that no technologically advanced extraterrestrial intelligence (ETI) has spread through the galaxy; but under commonplace assumptions about galactic civilization formation and expansion, this absence of observation is highly unlikely [2]. Under those assumptions, intelligent life that is thousands or millions of years more advanced than ours should be common, and should have had ample time to spread out to every planetary system in the galaxy, even at humanity’s current speeds of space travel [3]. So where are they?
Recently, the Fermi Paradox has received increased attention after a number of discoveries including that earth-like exoplanets are common [4], which has contributed to a renewed academic interest in the search for ETI [5].
Solutions to the Fermi Paradox
Many solutions to the Fermi Paradox have been proposed. It has led some to conclude that humans are the only advanced civilization in the galaxy, either because civilization formation is very rare, or because intelligent civilizations inevitably destroy themselves [3], [6], [7].
Another category of solutions are those in which ETI are indeed common, but due to their behaviour we do not detect them. For example some propose that ETI could not easily get here [2], or would not want to come [3], [8]. Others propose that ETI may be present but typically remain hidden – because we are in a zoo [9], or planetarium of their design [10]. More recently, some have proposed that ETI are common, but for essentially game theoretical reasons typically remain hidden (e.g. due to the risk of being attacked [11], [12]). Such game theoretical approaches to explaining ETI behaviour are appealing because they are potentially universal, explaining why all groups of ETI would have a given behaviour, as opposed to relying on (for example) coincidence that all groups choose not to travel. We build on this type of approach by exploring a related but different game theoretical, behavioural solution to the Fermi Paradox.
Will ETI be indifferent to detection?
The conclusion that because we have not detected ETI, they do not exist, or would not travel here, contains implicit assumptions about the nature and pattern of ETI. In particular, a common assumption in such arguments is that ETI would be indifferent about use detecting them, and not purposefully try to avoid it [3]. The vast majority of practical research involved in searching for ETI rests on this assumption (e.g. [13], [14]).
But a closer look at they way terrestrial civilisations interact (and the game theory that dictates it) suggests there may be problems with this assumption.
In short, spying and secrecy are extremely common.
The conditions that prompt spying and secrecy (i.e. covert intelligence) are defined by game theory, and are very simply satisfied: In any game of imperfect or incomplete information where decisions are made in advance (e.g. rock paper scissors, poker, battleship; business, sport, war, international relations, etc.) there will be an incentive to spy on other players, and keep them from spying on you [15], [16]. For example, consider the children’s game of rock paper scissors: If I have foreknowledge of the strategy you are going to play, I will always win. This immediately creates an incentive for me to spy on you to find out. In turn, this creates a incentive for you to keep information about your strategy secret from me (and vice versa). This dynamic creates an arms race for information (e.g. [17], [18])
similar to those observed in evolutionary biology and elsewhere [19]–[21].
The simplicity of the conditions that incentivise covert intelligence contribute to it being widespread. Throughout human history, covert intelligence is practically ubiquitous, has arisen multiple times independently [22], and today is considered a necessary function of government [23].
Although the conditions to enable covert intelligence are simple, the subsequent behaviours it incentivises are not. For example, in Rock Paper Scissors, if I do get foreknowledge the move you intend to play but you find out that I know, then my knowledge becomes useless – so there is also an incentive for me to keep my spying on you secret, and for you to feed me false information, etc.. Furthermore, if I know that you know that I know your strategy, then I can still gain advantage – but what I should play depends on whether you know that I know that you know that I know… and so on: I am forced to model infinite hierarchies of knowledge and beliefs [16]. The resultant hall of mirrors is highly prone to deception and is notoriously difficult to navigate [23].
The ubiquity and nature of covert intelligence is also often underappreciated. There is a well documented gap in its history and academic literature [24]. For example, the Christian Old Testament (the Jewish Tanakh) contains more references to spies than any history of Britain or of most other countries [22]. This gap has been created by a number of factors, including the inherently secret nature of covert intelligence, a lack of appetite from governments to fund public study of it, and general confusion arising from fictional portrayals [22], [23]. On this latter point David Omand, the former head of the UK’s signals intelligence agency notes “In considering public views of intelligence and security we are dealing with a magical reality, a psychological construct, not direct portrayals of the real world [23]”.
Secrecy, lack of study and fiction may contribute to why covert intelligence has been neglected as a solution to the Fermi Paradox.
Objective of this paper
Given its ubiquity on Earth, covert intelligence could perhaps be common amongst ETI. If so, this could perhaps explain the Fermi Paradox.
In this paper we seek to understand if it is plausible that the cause of the Fermi Paradox is due to ETI covert intelligence. To address this ask two questions:
1. Is it plausible that advanced ETI in general would typically carry out covert intelligence (i.e. spy on, and attempt to remain hidden from) human-level civilisations?
We consider the game theory of covert intelligence, dynamics of knowledge races and common patterns of covert intelligence throughout history, to create a simple qualitative model to understand the conditions under which covert intelligence is likely to happen. We then input basic assumptions about ETI to qualitatively asses their incentives for covert intelligence.
2. If ETI were carrying out covert intelligence on Earth, would we know?
Next we conduct a thought experiment. We ask if ETI were carrying out covert intelligence against earth, (a) what patterns of evidence would this leave, (b) which of this evidence would be detectable and (c) which of it would identifiable by humanity. To address this question we build on the previous model by considering relevant and common patterns of covert intelligence evidence, detection, identification and methods throughout history. The output constitutes a set of observationally testable predictions for ETI spying.
Results
We find that it is a minimum plausible that ETI will typically remain hidden from, and spy on, civilisations at humanity’s level of development, for basic strategic reasons. This questions the common assumption that ETI will be indifferent about being detected. It poses a solution to the FP that we name the Covert intelligence Hypothesis:
| The Covert intelligence Hypothesis: Advanced ETI will generally choose to remain hidden from, and actively spy on, human-level civilisations, because it will be commonly be in their strategic interest. This routine use of covert intelligence therefore explains the Fermi Paradox. |
We also find that in the case of ETI spying, evidence of this activity would have likely been detected – potentially enough to correctly identify the cause as ETI – but that the scientific community in general would be unlikely to be aware, in part due to the deceptive nature of the evidence being largely incompatible with the strict scientific method. We propose a set of observationally testable predictions, and suggest a methodology by which they could be tested.
Assumptions
This work rests on the following assumptions:
- The solar system not special: intelligent life is common in the galaxy, and much of it is thousands or millions of years older than humanity
- Advanced ETI are rational decision makers (i.e. subject to game theory), commonly develop interstellar travel capabilities, and typically spread out across the galaxy
- We are unaware of ETI
We therefore limit our analysis to ETI expected by these assumptions, i.e. ETI who:
- Are already in the vicinity of the planetary system containing a human-level civilisation (i.e. are either on the planet already, or can travel to it in days / weeks);
- have been in the vicinity for a long time (~thousands of years or more);
- are thousands or millions of years more technologically and scientifically advanced than humanity.
We also allow for the fact that there may be multiple groups of different ETI who have reached any given planetary system.
Is this scientific?
Spying is not a common subject in science. This raises the question: Is this scientific? The key criteria for a scientific hypothesis is falsifiability [25]. All of the analysis in this paper is simply falsifiable: Should any of the above assumptions be disproved then it will fall. It is also verifiable: We present observationally testable predictions, and outline methods for testing.
However, covert intelligence necessarily involves conspiracy, which is commonly dismissed out of hand in science. Should we dismiss the possibility here, too? The dismissal of conspiracy was originally suggested by Popper [26] – not because conspiracies do not exist, but because they are hard to carry out. Popper’s approach is a heuristic rule, to be applied where it is appropriate. For most of science, where the subject of study is most often realistically incapable of conspiring against the scientist, this is a very useful and time saving approach. (E.g. it is not worth considering the possibility that your odd data on butterfly migrations is because the butterflies are conspiring against you). But in covert intelligence, conspiracies are necessary, and often the default [22]. (E.g. It certainly is worth considering that your odd data on German U-Boat movements is because the German High Command are conspiring against you). Therefore, in this case, Popper’s heuristic is inappropriate: Pre-dismissing conspiracy when it is an extremely unlikely and potentially unfalsifiable possibility (as in most science) is very helpful; Pre-dismissing conspiracy when it is a common and important component of the field is not – and doing so runs a significant risk of type 2 statistical errors (i.e. false negatives).
In a sense, this odd juxtaposition highlights the unique nature of the Fermi Paradox. The existence of ETI is such a vital question when trying to understand the universe that it very clearly aligns with the goals of science, and therefore, whatever the answer to that question is, it must also be worth studying scientifically. But given that we know absolutely nothing about ETI, how can we know if science is an appropriate tool to use to search for it? If we assume ETI will be similar to most subjects that science typically studies (i.e. indifferent or incapable of deceiving the investigator), then science surely is the ideal tool. But what if ETI does not fall into this category, and instead, like most guilty parties in a criminal trial, or child spying on their opponent’s cards, is sophisticated enough, and motivated enough, to present an intentionally deceptive set of data? The scientific method is not configured to cope with such intentional deception (Figure X), which may be why it is not, for example, used to decide guilt in court. Therefore there is a risk we may use an inappropriate tool, and come away confidently (and perhaps incorrectly) saying that ETI does not exist. In the unique case of the Fermi Paradox, an awareness of the limitations of the scientific method may be valuable.
Finally, a related question is: Would such advanced ETI, even in theory, be detectable? The extent to which covert ETI are detectable obviously depends on their capability. In the case of ETI who are omnipotent with respect to our current capabilities ( we term this “relatively omnipotent”), we would not be able to detect them, and so this case of the hypothesis is untestable. (It is still falsifiable, as described above.) However, to constrain the problem to testable predictions, we limit our analysis to ETI who are not relatively omnipotent. If ETI are indeed common, it may be that there are many groups, and some may fall into either category.
Layout of this paper
In section 3.1 we address the question of the extent to which ETI covert intelligence would be incentivised. We discuss some basic principles of covert intelligence (section 3.1.1), game theory of covert intelligence (section 3.1.2), cost-benefit analysis (section 3.1.3), dynamics of knowledge races (section 3.1.4), basic assumptions about ETI (section 3.1.5), and combine those into an analysis of ETI incentives for covert intelligence (section 3.1.6).
In section 3.2 we address the question of whether the scientific community would generally be aware if ETI were carrying out covert intelligence on Earth. We look at the history of covert intelligence, and discuss common and relevant patterns of evidence (section 3.2.1.), and patterns and methods of detection (section 3.2.2) and identification (section 3.2.3). We then present predictions of what we would expect in the case that ETI were carrying out covert intelligence, focusing on evidence patterns (section 3.2.4), detection patterns (section 3.2.5) and identification patterns (section 3.2.6). We summarise these results in section 3.2.7.
In section 4 we discuss implications, limitations, and how our predictions could be tested, and in section 5 we present concluding remarks.
3. Models, Results and Predictions
3.1 Would ETI spy?
There is no fully developed framework that describes in detail when and how covert intelligence will happen [27], [28]. Therefore, to assess the potential for ETI covert intelligence we develop a crude qualitative model below, which is informed by general principles of covert intelligence, game theory, the dynamics of arms races / knowledge races, and cost-benefit dynamics.
Some basic principles of intelligence
Firstly, intelligence is not magic, nor is it mythical. It is simply the process of satisfying a basic need for information to reduce ignorance . Rather like any other information gathering and processing activity, intelligence activity involves collecting information about the world and using it to inform your model of the world – to better understand what is happening, why it is happening, and trying to predict what will happen next. The general goals of intelligence are situational awareness and foreknowledge, which provide decision advantage, acting as a force multiplier [22], [23], [27], [29].
As briefly discussed in the introduction, perhaps the most confusing parts of covert intelligence are caused by its adversarial nature: You are often trying to predict someone who is at the same time trying to predict you, and so there’s a potential infinite belief and knowledge hierarchy of what you know, what they know, what you think they know, and what you think they know you know, and so on [16]. As a result, there’s an incentive for keeping what you know secret (stealth), and for finding out what they know in secret (spying) [23]. This creates a arms race for information.
To explore some basic principles of intelligence, we will return to a toy example – playing cards. Although only slightly more complex than Rock Paper Scissors, playing cards has sufficient complexity to demonstrate some key intelligence patterns. (However, in some instances the complexity of the real world generates behaviours that are not obvious in such toy examples, so we will be forced to sometimes consider real world patterns instead).
Collecting information is often difficult
Imagine you are playing any card game where you have a set of private cards that you can see, but your opponent cannot (e.g. poker, rummy, bridge, etc.). There is a incentive for you to spy on your opponent to gain foreknowledge of their actions, to help you win. But a key difficulty of collecting secret intelligence is that your opponent is typically seeking to prevent you from accessing their secret information: They are keeping their cards close to their chest. An added difficulty depends on the type of information you are trying to access. In intelligence, information is often divided into capabilities (e.g. what cards do they have?) and intentions (e.g. what do they intend to do with those cards?) [29]. Spying on either type is difficult:
“There can be no perfect foreknowledge. Secrets are hard to find out, mysteries are hard to assess, and complexities involve second- guessing the moves of one’s own side”. [23]
But spying on intentions is often more difficult, especially as this information often only resides inside your opponent’s head, and can change in an instant:
“Even the most sophisticated intelligence breaks down when confronted by the whims and vagaries of the changing human mind.” [23]
Despite the ephemeral nature of intentions, they can be extremely strategically important. For example: Are the Russians planning to launch their missiles, or not?
Secrecy and spying incentivise each other
In your card game, just as you are incentivised to spy on your opponent, you are also incentivised to keep your cards secret from them, and repel their efforts to spy on you. But even this effort of secrecy incentivises spying, because to stay secret, it very much helps to know your opponent’s capabilities of spying, so that you can mitigate them – which often requires spying on them to find out [17], [29]. Similarly, there will be an incentive to keep your efforts to spy on your opponent secret – even ignoring any punishment, it is simply easier to spy on someone if they are unaware that you are doing it; also, when spying on intentions, information is often only valuable if your opponent is unaware that you know it.
Secrecy is only worthwhile for information that is not known to the other side.
Another obvious point is that it is only worth trying to keep the cards hidden that are not publicly known (in game theory terminology: common knowledge [16]). For example in some forms of Poker there are public cards (face up) that are known to everyone, and private cards for each player. This explains why for example in the modern world spying and secrecy only occurs on a small subset of information – not because spying is an inherently marginal activity, but because most information is common knowledge (e.g. there is no benefit for the US to try to keep wheels, steam engines or or the location of South America from China, because they are publicly known).
In short, the amount of private information defines how much scope there is for secrecy and spying. If there is no private information, then there is no benefit to secrecy at all. And vice versa, if all of your information is private (as in many card games), then complete secrecy is incentivised.
Some private information is more valuable than others
When playing cards, it is often the case that learning of some of your opponents cards would be more valuable than others. For example in Poker, knowing that your opponent has the one card that could beat your hand is much more valuable than knowing which other cards they hold. In general, the more potential strategic loss information would cause if it fell into the hands of your opponent, or strategic gain it would give if captured, the more valuable that information, and hence the greater the incentive for secrecy or spying.
This is hard to generalise, but pieces of information that would cause very large scale impact if known (real world examples might include a recent discovery for workable nuclear fusion, how to break widely used cryptography, etc.) are likely to be of higher strategic value than those with low level impact (e.g. the engineering specifications of a now defunct technology).
Arms race dynamics
The incentives of covert intelligence create a arms race for information in which what matters is the marginal amount of advantage over your competitor, and not your absolute capability. You may have highly sophisticated methods of spying on your opponent in cards, but if their methods of secrecy are more advanced, your efforts will probably count for nothing. As such, a typical pattern of covert intelligence (arms races generally) is that of tit-for-tat improvements in response to improvements of the other side (e.g. improvements of detector capabilities of one side in response to improved stealth of the other) [17], [19], [21].
There is often an incentive to spy even without a strategic target
Let us imagine your have been playing cards against your opponent, and each spying on the other, for some time. You know how your opponent spies on you, and you have methods to effectively counteract it. You might therefore be tempted to stop spying on how they spy on you, because you already know the answer, and it takes constant effort. But in this case, how will you know if they start doing something different? Worse, what if they start doing something entirely new that you didn’t expect, like conspiring with another opponent?
The nature of having incomplete and imperfect information means that you don’t know what you don’t know (and so can be helpful to try to find out things, even if you don’t know what you’re looking for). This was famously articulated by Donald Rumsfeld: “There are known knowns; there are things we know we know. We also know there are known unknowns; that is to say we know there are some things we do not know. But there are also unknown unknowns—the ones we don’t know we don’t know. And if one looks throughout the history of our country and other free countries, it is the latter category that tends to be the difficult ones”. [30] The risk of change, and unknown unknowns, provide a common incentive to spy even in the absence of known strategic target [16], [29].
Mostly, everyone spies on everyone, always
In a similar way, in the Art of War Sun Tsu explains that intelligence is not just for war, but is highly valuable in peacetime, as an investment in early warning in case of a threat or opportunity [1], [29]. Spying is also not reserved for powerful enemies (in the modern world, practically all countries spy on all others, including their allies [22]); neither is it purely about short term solutions:
[Governments use intelligence] not just to be able to make predictive judgments about the future course of events, but to realize what the world would then look like so as to be able to identify and start to implement policies and partnerships now that would mitigate the risks to society of such trends.
Although Chess contains no private information, it is perhaps a more relevant toy example in this case than playing cards, as like international relations, it is highly strategic and contains many interdependencies. To become a chess grandmaster, it is vital to consider the potential moves and strategic impact of all of the pieces (including those that that currently pose no direct threat or opportunity) –not just the most powerful, or currently important. Many chess games have hinged on the actions of a single pawn, just as many seemingly unimportant countries have at times become highly strategically valuable [22], and so a common approach is to collect intelligence on all of them.
Technology races and covert action
Not all covert activity or intelligence is about decision advantage. For example,
commonly the target of intelligence gathering is technology (e.g. how to make nuclear weapons, or advanced stealth, etc.) [22]. Such information can simply provide capabilities advantage, as opposed to decision advantage. In addition, some covert activity is less about gathering intelligence but more about covert action – i.e. actively attempting to change the course of events by unattributable action [29]. This falls under the same general umbrella of covert actions incentivised for simple strategic reasons.
Covert intelligence appears to be an emergent behaviour
Given that a simple card game can incentivise covert intelligence, it is perhaps not surprising that is appears to be an emergent behaviour in the history of civilisation. Occasionally in the past, some states have, for various reasons, shunned covert intelligence. This has mostly happened either where states are so large and powerful they can win battles with brute force alone, without the force multiplier that intelligence provides (e.g. China during the 18th-19th centuries), or where for ideological reasons, covert intelligence is seen as distasteful (e.g. in ancient Athens). In all of these recorded cases, following some disastrous losses, covert intelligence was reinstated [22].
The Game Theory of covert intelligence
Game theory is the study of mathematical models of strategic interaction among rational decision-makers. It has been widely used to successfully predict the dynamics of social system across different types and substrates. [16]
There is relatively little work on the game theory of intelligence, but models have shown that the requirements for covert intelligence are very simple: It is incentivised in games of imperfect or incomplete information, and is subject to cost / benefit calculations (e.g. [15]). Imperfect information games are those where players have only partial knowledge about the current state of the game, such as Poker or Battleship, and incomplete information games are those where players have only partial knowledge about the opponents utility function, such as auctions. Most real world situations fall into both of these categories – for example, sport, business, politics, war, international relations, etc. [16], [29].
Although games are inherently cooperative, they do not always result in hostility. Many games spontaneously produce highly cooperative behaviour to reach mutually beneficial solutions, and game theory has been a central tool in understanding how cooperation can happen [31], [32]. In a similar way, the results of covert intelligence is not always hostile, and can result in mutually beneficial solutions for both sides (e.g. giving advance warning of disagreements and giving time for diplomatic solutions.) [23]
Cost / Benefit Analysis of covert intelligence
There is an economic aspect of covert intelligence. Even if covert intelligence is incentivised, if the costs outweigh the benefits it will not be the rational decision. We outline some of the simple factors affecting the cost / benefit below.
Benefits
We have already discussed the benefits of covert intelligence at length. In general, the bigger the potential strategic benefit of covert intelligence, the greater cost can be justified.
Because with ETI we are considering a highly advanced opponent, a relevant factor that affects the level of benefit is knowledge asymmetry. The greater knowledge asymmetry in your favour, the more decision or capabilities advantage you have to lose, and hence in general the more incentive there is for you to maintain that asymmetry – i.e. the greater the incentive for secrecy. (This likely also increases your incentive to spy on your opponent in a defensive manner to understand and defend against their attempts to spy on you.) In the same way, the greater knowledge asymmetry in your opponent’s favour, the more potential benefit there is from removing that asymmetry – i.e. the greater the incentive for spying (and also to keep that spying, and your capabilities for spying, secret) [33].
Costs
Two key contributors to the cost of covert intelligence are risks and capabilities. Risks of secret intelligence include outcomes such as punishment from being caught, exposing your capabilities (etc.). The greater the risk, the greater the potential cost.
Capabilities refer to your own capability at conducting covert intelligence operations. They include logistics, stealth, detection, modelling, analysis, and the level of knowledge you have about your opponent. In general, the greater capabilities asymmetry in your favour, the lower the cost of covert intelligence, and vice versa. For example, the US’s cost of spying on Afghani opium farmers without being detected is probably relatively small, because the US already have highly advanced satellite and drone technology than can simply be redeployed to the area. Meanwhile, the farmers may only have only rudimentary tools to detect the spying, and limited logistical capabilities to react to it – making secrecy a relatively low cost task for the US, given their existing capabilities. On the other hand, although there would be potentially a huge amount to gain for Afghani farmers to access the military and commercial secrets of the US, the huge capabilities asymmetry against them in terms of accessing, understanding and using that information may mean that the cost of success is probably prohibitive.
Capabilities constrain the scale of SS
Capabilities also partly constrain the scale of covert intelligence possible. For example, in the 19th century is was generally thought that only tactical (i.e. small scale) surprise was possible in war, because of the lack of logistic capability to mount a strategic (i.e. large scale) offensive. However, with the industrialisation of war and invention of the railway, telegraph (etc.), the scale of possible deception increased dramatically, and strategic surprise became possible [23]. In general, greater capabilities enable larger scale operations.
How do we use this to tell if ETI will spy?
In table 1, we collect the qualitative factors described above to assess the plausibility of ETI spying. We assess a known positive case (modern day US / China international relations) and two known negative cases (human / chimpanzee interactions, and human / C. Elegans interactions.)
Basic assumptions about ETI
To use as an input to the model, we make the following basic assumptions about ETI. These reflect the general scope of the paper stated in the introduction. (For simplicity we describe the interaction as ETI / Humanity, but the assumptions are mostly general, and so the results may apply generally to interactions between ETI and Human level civilizations.)
ETI are:
- Capable of building technology to enable interstellar travel to earth
- Thousands or millions of years more technologically advanced than us
- Are already in the vicinity of earth, and have been for thousands of years
And
- We are unaware of them
Results
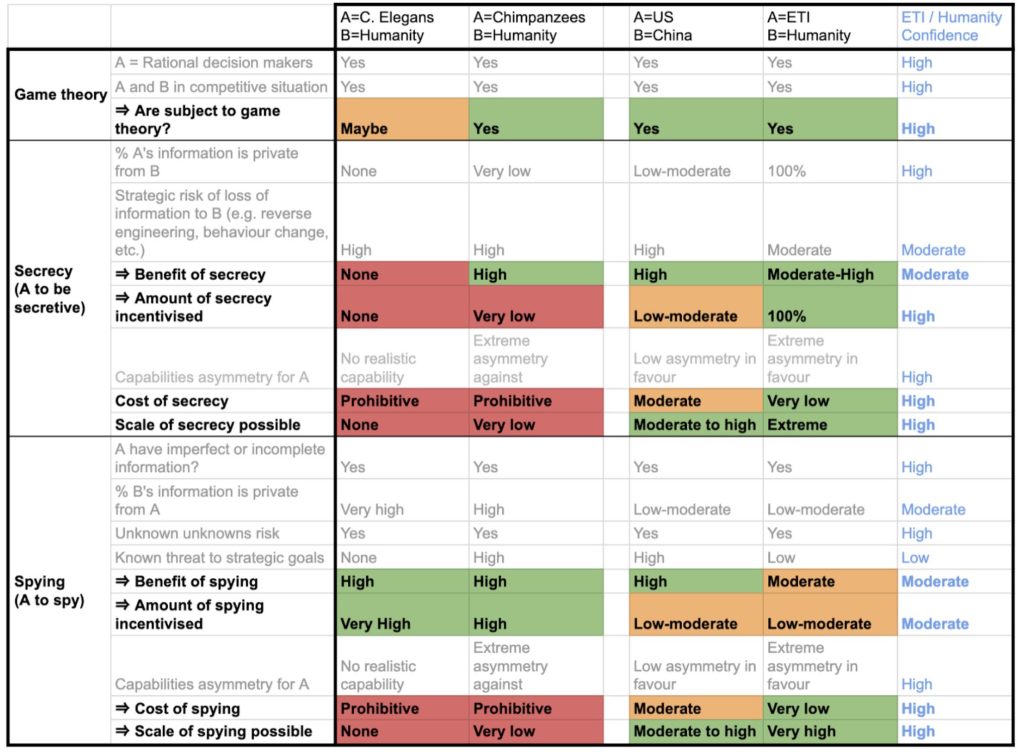
Table 1. Analysis of incentives for ETI spying and secrecy.
- C. Elegans / Humanity
Covert intelligence in general
- C. Elegans is simple nematode worm that has been widely studied as a model organism [34]. Despite their simplicity, C. Elegans have been shown to be rational decision makers [35], have imperfect and incomplete information, and are in a competitive evolutionary situation with humanity in which decisions that affect them are often made in advance. They therefore seem to fit the basic needs to incentivise covert intelligence.
Secrecy
- C. Elegans have practically no information secret from humans, so there would be little benefit to secrecy, and they also have no real capability for secrecy, so the cost would also be prohibitive.
Spying
Meanwhile, there is a great deal of human information not accessible to C. Elegans that in theory would be of great strategic benefit – but C. Elegans do not possess any real capability of collection or analysis, and so the cost of spying is absolutely prohibitive.
Summary
Overall the framework predicts that that C. Elegans will not spy on, or remain secret from Humanity, mostly due to prohibitive costs caused by lack of capability.
Chimpanzees / Humanity
Covert intelligence in general
Chimpanzees may be largely rational decision makers [36], have imperfect and incomplete information, and are in a competitive evolutionary situation with humanity (with high capabilities asymmetry against them), in which decisions that affect them are often made in advance. They therefore mostly fit the basic needs to incentivise covert intelligence.
Secrecy
Chimpanzees probably have very little information currently secret from humanity, and also have very limited capabilities for secrecy, and so any benefit is likely limited, and the cost prohibitive.
Spying
There is a great deal of potentially strategically useful information about humanity that chimps do not have, some of which is intentionally kept hidden (from other humans, but the impact is the same). They are also at risk of unknown unknowns with respect to humanity – and so there is an added issue of not knowing if humanity have developed new capabilities or intentions that could cause strategic damage to the goals of chimpanzees. As a result, there is a large theoretical benefit to spying. However, although not completely negligible, chimpanzees have very limited absolute capability to collect, understand and act on this information compared with humanity, and so the cost of spying is prohibitive. In addition, there is very large logistical capabilities asymmetry in favour of humanity, so the scale of any spying or secrecy possible would likely be very small, probably limited to a few short term actions of a single chimp.
Summary
Overall the framework predicts that that Chimpanzees will not spy on, or remain secret from humanity, mostly due to prohibitive costs caused by lack of capability.
USA / China
Covert intelligence in general
The USA is composed of predominantly rational decision makers; it is in a competitive situation with China, has incomplete and imperfect information, and many decisions that affect it are made in advance.
Secrecy
Although only a relatively small proportion of the US’s total information is private from China (e.g. policial intentions, new military technology, etc.) as most is common knowledge (e.g. existing technology, such as electricity, microprocessors, hydraulics, etc.; most scientific research, most social and demographic data, etc.), there is significant strategic risk involved with sharing that private information, and so the benefit of secrecy is high. The US may have a small covert intelligence capabilities asymmetry in their favour (or perhaps it’s nearly zero, or even negative), meaning the cost of secrecy is perhaps moderate. The US also have good absolute logistic capabilities, so the scale of secrecy operations they could mount may be reasonably large, perhaps up to grand strategic movements of hundreds of thousands of people or more.
Spying
The case with spying is similar: Although there is probably only a relatively small fraction of China’s total information that is not known to the US, knowing this information (especially if China were not aware) would likely impart significant strategic benefit to the US. So the benefit of spying on this information is high, and due to the small capabilities asymmetry, the cost is likely moderate. Again, due to their relatively high absolute level of logistical capabilities, intelligence and information processing capability, the US may be able to successfully carry out quite large scale spying operations, perhaps up to grand strategic in nature.
Summary
Overall the framework predicts that that the USA will expend significant effort in spying on China’s private information, and in keeping their private information secret from China – and that due to the US’s advanced logistic capabilities, there is scope for large scale secrecy and spying operations.
ETI / Humanity
Covert intelligence in general
The ETI we are considering are by definition intelligent, and, if they are able to build interstellar spacecraft, seemingly must be capable of rational decision making. If we assume they have spread across the galaxy, then they must occupy a somewhat overlapping space with humanity, and so must, to some degree, be in an evolutionarily competitive situation with us. Given that these ETI are not relatively omnipotent with respect to humanity, they must have imperfect and incomplete information. As such, ETI would satisfy the minimum conditions to incentivise covert intelligence.
Secrecy
Given that we are unaware of ETI, then we can assume that if they exist, 100% of their information would be private from us. This would give ETI a very large strategic advantage (we could not hope to outmaneuver them if we did not know they existed, let alone know their capabilities or intentions; it would also mean that we couldn’t spy on them, or act to intentionally confuse them, which would make it much easier for ETI to predict our actions). Therefore, if ETI divulged any of their information to us, including their existence, this would have the potential to be strategically damaging to them, and so would incentivise total secrecy. In addition, given the likely age of any such ETI, they would certainly be significantly more technologically advanced than us, giving them a very large capabilities asymmetry in their favour. Unlike C. Elegans or chimpanzees, humanity have a basic absolute capability of scientific enquiry and reverse engineering. Although much of ETI technology would perhaps be beyond our comprehension, it is hard to imagine that none of it would result in new discoveries and technical advancements (or for there to be no scope that we could pass the information on to some other ETI group who could use it). As a result, there may be moderate, or even significant risk of ETI losing some of their capabilities asymmetry if any of this private information were accessed by humanity. Meanwhile, given the likely extreme capabilities asymmetry in favour of ETI (both in terms of detection / stealth and logistics), the cost of ETI secrecy would likely be very low, and the scale of secrecy operations that ETI could mount would likely be extremely large. Taken together, this suggests a moderate to high benefit of ETI secrecy at very low cost, and an incentive for that secrecy to be total.
Spying
If we assume any covert ETI would have been in the vicinity of the solar system for a long time, then it may be that much of humanity’s information would already be known to them, and so if spying were incentivised at all, it would likely be limited to the small fraction of private information. Given that such ETI were not relatively omnipotent, there would be scope for humanity to have some private information from them. Also, given in recent decades that there has been a recent dramatic increase in the amount of information humanity is trying to keep secret (from itself), and a similar dramatic increase in the sophistication of that secrecy – it seems possible that despite the long time ETI would have been present, today a low to moderate (and increasing) amount of that information perhaps would be private from ETI, unless they made active effort to access it.
This information private from ETI would by its nature tend to contain high level strategic intentions, advanced and large scale military capabilities – and so if the actions of humanity were of any strategic impact to ETI, there would be an incentive to spy to access this information. However, given the size of the cosmos, and the likely age and sophistication of such ETI, it generally seems unlikely that humanity would represent a high strategic threat or opportunity. But even if humanity had no strategically valuable private information at present, a number of factors would still incentivise a limited amount of early warning, background intelligence gathering. First, to provide early warning in the case that humanity become strategically important in future; second, the risk of unknown unknowns; and third, the risk of undetected changes in our capabilities or intentions. This point may be particularly relevant, because given the strong incentive for ETI secrecy, keeping abreast of humanity’s improvements in detection capabilities would perhaps have significant value.
Given the likely extreme capabilities asymmetry in favour of ETI, the cost of such spying would likely be very low.
Summary: Would ETI Spy?
Overall the framework predicts that that:
- ETI would be have / highly incentivised to remain secret from humanity, there would be incentivised for this secrecy to be total, and they would likely be capable of such secrecy at very low cost;
- ETI would have low to moderate benefit of spying on humanity (even if we don’t currently represent a significant strategic opportunity or threat) at very low cost.
In summary, we find it as a minimum plausible that advanced ETI in general would typically opt to remain hidden from, and actively spy on, human level civilisations, for strategic benefit.
This analysis provides support for the covert intelligence Hypothesis: There may be potentially numerous ETI in contactable range, but their default behaviour towards a civilisation at our level of development would be clandestine for strategic reasons (especially given the likely capabilities asymmetries).
3.2 Would we know?
This section is a thought experiment. We focus specifically on Earth, and ask: If covert ETI were here, and had been spying on us for thousands of years – (a) what would the evidence look like, (b) to what extent would we have likely been able to detect it, and (c) to what extent would we have been able to correctly identify it?
To address these issues, we build on the model from section 3.1., also considering common and relevant patterns of intelligence evidence, detection, identification from modern day and the historical record. As much as possible, we focus on patterns that are general in the sense that they occur across substrates, cultures and throughout history.
Patterns of covert intelligence
Evidence patterns
- Non reproducible evidence
Because covert intelligence is a knowledge race, as a covert player it is very useful to know if you have been detected, because it signals that your stealth methods and tactics may not be sufficient to keep you hidden. Once detected, players typically change their methods and tactics to make sure they are not detected in the same way again (e.g. [17]). The result is that by default, evidence in intelligence is often non-reproducible. In general, the greater the capabilities asymmetry in favour of the covert actor, the more likely they will be aware of being detected, and hence the more likely any detection evidence is to be non-reproducible.
- Mistakes
Mistakes are a universal pattern in the history of intelligence. These include technical failures, unexpected interactions, miscalculations (etc.) and stem from incorrect assumptions, unreliable technology, imperfect and incomplete information, among other factors. (If you had complete and perfect information, there would be no need to spy, and so mistakes are in that sense unavoidable). We could find no clear overall pattern of a decrease in covert intelligence mistakes with increased technical sophistication. As is common in other fields, most mistakes are small, a few are large, and rarely, some are catastrophic [22], [23], [29].
Another category we include as mistakes are when, due to unforeseen events, other priorities become more important than the need for stealth (e.g. if the operation is attacked, if a more valuable opportunity arises at short notice). We also include as mistakes situations where secrecy is sacrificed due to the intentions of individuals becoming misaligned with those of the wider group (e.g. intentional leaks, or when the lives of the individual operatives are at stake, etc.)
- Spatial and Temporal Distribution
Covert intelligence is not evenly spatially or temporally distributed. It is often concentrated towards places or times with a high concentration of strategically valuable information (e.g. sensitive military or intelligence locations, at times of political crisis, war, etc.), and also, as much as possible, in times or places that make detection more difficult (e.g. at night, in more remote locations). However, there is also typically a broad background of intelligence spread more indiscriminately across space and time, that continues during peacetime. This type of background intelligence commonly acts as an early warning system to identify emerging threats and opportunities [22], [29].
Detection patterns
- Marginal detection pattern
Because intelligence incentivises a knowledge race, detection and stealth capabilities are often finely balanced, with improvements by one side being met with improvements of the other. Both sides will typically be closely monitoring advances in the other’s capabilities so they can get, or stay, ahead. As a result, detection events are commonly marginal, because the technology is often working at its limit, and remain marginal even as the level of technology improves (e.g. [17]). Intuitively, the greater the asymmetry in favour of the covert actor, the more likely any detection event is to be marginal (and vice versa), because the limit of detection is likely to be further away from the capability detectors; this gives the covert actor more buffer to cope with mistakes, more time to become aware of potential detection events and fix them before they happen, or before they progress beyond marginal (figure 1).
- Arms race detection pattern
The arms race (knowledge race) nature of intelligence also creates a common pattern of tit-for-tat upgrades. For example, in a detection / evasion knowledge race, the following pattern is often observed [17]:
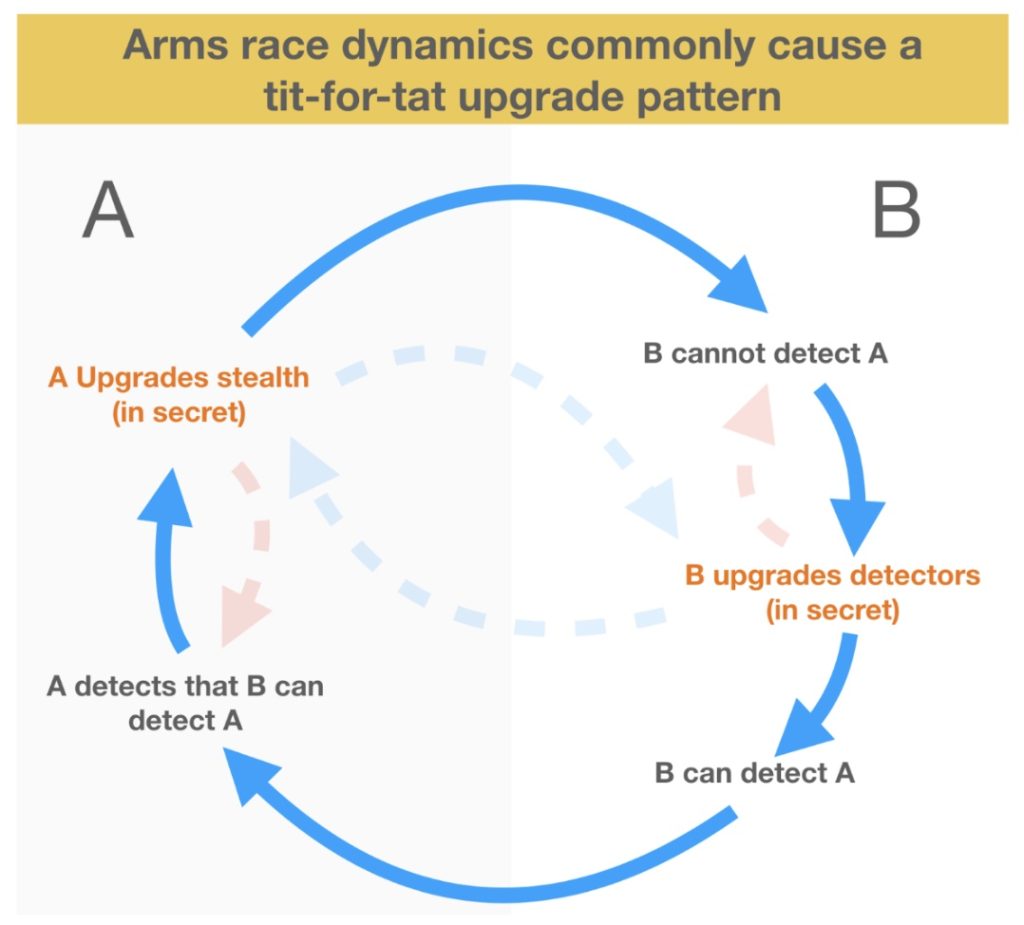
Figure 1. A and B are opponents in a detection / evasion arms race. A repeating tit-for-tat pattern of upgrades in detector sensitivity and stealth occurs. A’s upgrades must be carried out in secret (without the B’s knowledge) otherwise there is a risk that B will also upgrade before A’s upgrades can be deployed (blue dotted lines; the same also applies to B’s upgrades). In this case no advancement in the arms race will occur. Also, if A’s stealth capabilities are far in advance of B, then B’s upgrades will still not cause detections (red dotted lines; the same applies to A’s upgrades). This diagram is a simplification – in reality often both detection and evasion arms races between A and B will occur in parallel.
The right hand portion of the diagram shows the resulting evidence pattern from B’s perspective: Initially, there are no detections of A; then, after B a secretly upgrades their detector capabilities, there is a temporary period where detections of A are common; eventually these detections stop because A has upgraded their stealth in response [e.g. spycatcher]. This pattern then repeats when B releases another upgrade of detectors, and so on.
There is obviously a strong incentive to keep any upgrade of stealth or detector capability secret from your opponent, as if they learn of your upgrade plans, they may be able to eliminate your advantage before it is deployed. Should this happen, in the above sequence there are no detection events after B deploys new detectors, because A has already upgraded to avoid them in advance (blue dotted lines) [e.g. spycatcher].
This tit-for-tat pattern requires both sides to have a sufficient level of capability. For example, if the stealth capabilities of A are far in advance of B, then B’s detector upgrades (even if kept secret) will typically not be enough to create any consistent period of detections of A, because even after upgrade they are not close to approaching the sensitivity of detection needed, and no tit-for-tat pattern will be observed (red dotted lines).
- Agents of detection
Because of the arms race nature of intelligence, detection typically happens at the state of the art. As a result, most detection events, and a greater proportion of those with clearer evidence, are achieved by experts who are specifically looking for covert intelligence (e.g. military and intelligence agencies). Another reason for this bias is that intelligence experts also tend to focus their search on times and places where covert intelligence is concentrated (e.g. near strategically sensitive material) [17], [18], [29].
Rarely, state of the art detection also happens accidentally by non-military or intelligence experts who are not searching for covert intelligence, but have state of the art detectors for other reasons (e.g. scientists, researchers, etc. – e.g. [37]).
Also because detection mostly happens at the state of the art, detection by laypeople is rare, and typically only happens in the case of mistakes, which again are mostly marginal. Because spying is typically concentrated near strategically sensitive information – which is often in remote, hard to access locations – this further reduces the opportunity for layperson detection. However, rarely, catastrophic mistakes do happen that are clearly detectable by laypeople [27], [38].
Identification patterns
- Agents of identification
As with detection events, the vast majority of accurate identifications will typically also be achieved by intelligence experts because (a) most clear detections occur at the state of the art, and (b) intelligence experts are more likely to have the appropriate analysis frameworks and relevant contextual information needed to make an accurate identification [23].
However, very rarely, catastrophic mistakes do occur that allow laypeople to strongly suspect, or even clearly identify that evidence is the result of covert intelligence. Such events tend to be both very out of the ordinary. For example, this could be due a major technical malfunction such as the crash of a strange looking spyplane [38], accidentally coming into possession of covert tradecraft (such as when, in 1953, a paperboy in Brooklyn was accidentally given a strange nickel by a Russian apartment owner the when dropped, flipped open, showing a secret compartment containing a roll of microfilm containing a cyphered code [39]) or an intentional leak of information that self-identifies as such (e.g. [40]).
- Analysis frameworks used for identification
Intelligence methods (i.e. various frameworks of critical analysis) are typically used for analysis of evidence, understanding and identification. Such methods routinely consider the possibility of deception, conspiracy and disinformation, as this is very common in intelligence situations. There are many approaches, but a general approach can be characterised as follows: Firstly the source of the information is analysed (e.g. provenance, historical reliability, intentions “cui bono”, technical capability to understand the information they are providing, whether the information is technically coherent, etc.), followed by generation of multiple hypotheses, and subsequent analysis of how closely the evidence matches what would be expected for each hypothesis (e.g. as part of the analysis of competing hypotheses framework [41]). The output is rarely a definitive answer, but instead a set of judgement statements about how likely various possibilities are, and the confidence / likely error in each [23], [29].
The scientific method is rarely, if ever used as the primary investigative framework for covert intelligence. It is however widely used as a lower-level tool (such as how forensic science is used as a tool in a criminal investigation, but is not used as the overall criminal investigative framework). This may be because the scientific method is not configured to consider the possibility of intentional deception or conspiracy (e.g. that the subject of investigation is intentionally trying to deceive the investigator), and so is vulnerable to being duped.
Specifically, science typically assumes the object of its analysis (a) will have reproducible behaviour, (b) is not capable of, or motivated towards intentional deception of the experimenter. The scientific method rejects non-reproducible phenomena [25], often dismisses outliers on the assumption that they are erroneous [42], and mostly rejects the possibility of conspiracy out of hand [26]. Therefore, using the scientific method to assess a deceptive subject runs a significant risk of type 2 statistical errors (i.e. false negatives – figure 2).
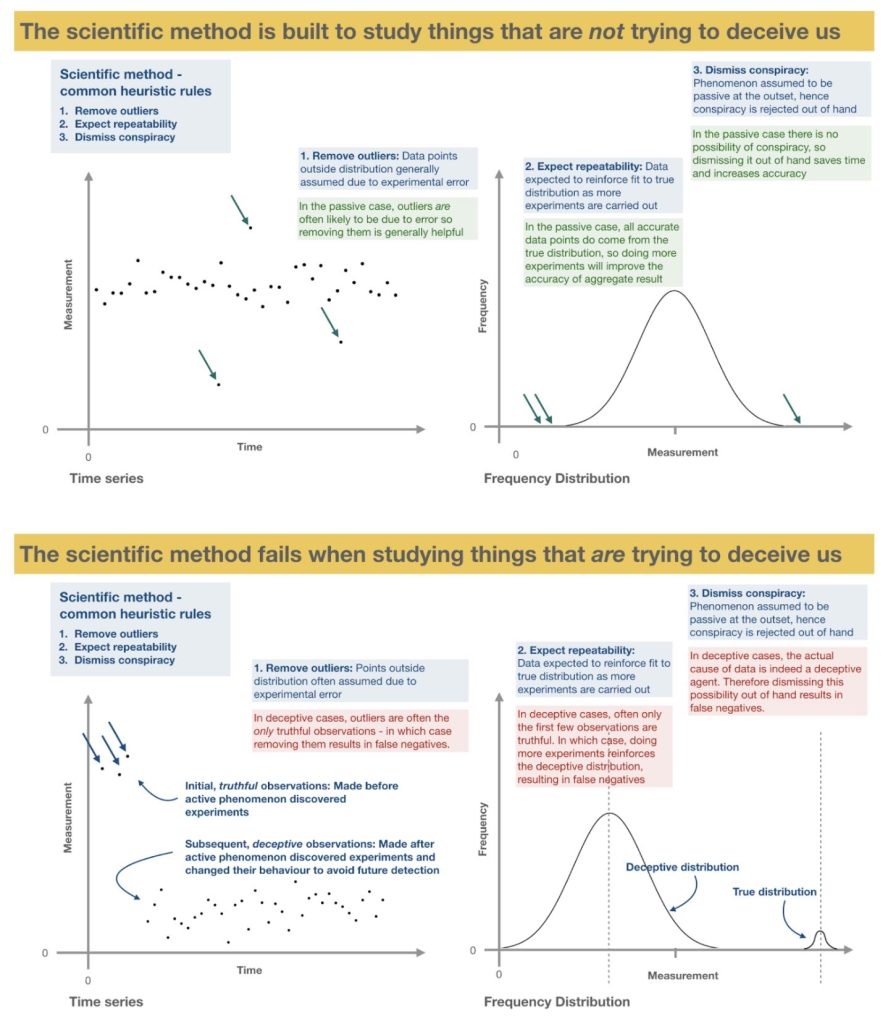
Figure 2. The scientific method encounters issues when studying a subject that is intentionally trying to deceive the investigator, that will frequently risk type 2 statistical errors (false negatives).
- The vast majority of successful identifications are kept secret
In the history of intelligence, it is extremely rare that any successful identification of opponent activity is made public (e.g [17], [40]). There is typically strategic benefit in not letting your opponent know that you have detected them, because this information could alert them to upgrade their stealth capabilities, or change their strategy. Those that are made public tend to be cases where there is particular scope for embarrassing your opponent [russia], swaying public opinion, or where catastrophic mistakes mean there a cover-up is not practical [22], [40].
When non-military experts (e.g. scientists, researchers) accidentally make high fidelity detection of opponent’s clandestine activity – despite the fact that they have no strategic reason to keep the information secret – before releasing the information, they often contact domestic military or intelligence agencies, to check that the detection is not sensitive (e.g. [37]). In most of these cases, it is likely those agencies opt to keep the information secret, for the same reasons as above.
- Even unambiguous detections are sometimes misidentified
Even when clear detections are reported directly to intelligence experts who have the skills and knowledge to identify them, sometimes the evidence is misinterpreted, lost, or ignored. For example, in US intelligence received detailed reports of plans the indicated a Japanese pre-emptive strike on Pearl harbour before it happened, but much of the evidence was rejected (in part because it did not fit with the prevailing US perception of what was possible at the time [29]).
Would we know? Predictions and analysis
Our analysis predicts the following patterns of evidence, detection and identification:
Evidence
Distribution: ETI covert intelligence concentrated around political and military sites that have strategic large scale impact, but with a separate, diffuse background activity globally.
ETI activity would be concentrated around the most strategically sensitive material (i.e. that with potential global impact, such as major military capabilities: chemical, radiological and nuclear weapons, repositories of high-impact political or environmental strategy, scientific and technological advancements, etc.), and at times and places of crisis, and concentrated in times and places of poor detectability (e.g. at night, poor weather, underwater, high altitude etc.) to minimise the risk of detection. Such crisis events may be ours (e.g. at times of war, or other global events) or ETI’s (e.g. at times when Earth for some reason has become more strategically important, such as where humanity have recently developed a step-change in capabilities which could have strategic impact).
At the same time, a lower, background level of diffuse, early-warning type activity would be expected across the globe, at a mostly consistent level since before the start of recorded history. Such activity would still likely be focussed in places where detection is less likely (e.g. remote areas, times of poor visibility, away from military or other advanced detectors, etc.). For the same reason, we would expect very limited activity over urban or built up areas due to the increased likelihood of detection, especially if urban areas are not near any strategically sensitive material.
Trends: Diffuse activity would remain constant through history, but focussed strategic activity might increase after the industrial revolution
ETI activity may have changed in pattern over history. Because humanity’s capability for large scale global impact actions has dramatically increased since the industrial revolution, we would potentially expect a parallel increase in targeted, strategic spying by ETI to keep up with the increased scale of activity. In which case, an initial pattern of predominantly diffuse, constant level background / early warning ETI activity would be joined after the industrial revolution by a significant ramping-up of targeted ETI spying on strategically sensitive material. Similarly, we would also expect an increase in ETI secrecy as humanity’s reverse engineering capability increased over the same period. On the other hand, it may be that ETI are so advanced, and humanity’s scope for meaningful global impact so limited even today, that our increased capabilities are of little impact – in which case we would expect only the diffuse, stable background activity.
Practically all ETI activity would leave non-reproducible evidence
In general, due to the extreme capabilities asymmetry in favour of ETI, practically all evidence of covert ETI would be non-reproducible, because it is likely ETI will be aware of any detections and make efforts to avoid them in the future. ETI would also likely make significant efforts to avoid leaving any unambiguous physical evidence (e.g. advanced technology, biological traces, etc.) as if captured, such evidence would make identification significantly easier. However, some risk may be unavoidable (e.g. when physical interaction is necessary, e.g. physical sampling, covert action, etc., or when catastrophic mistakes are made) which would leave some physical evidence.
Typical pattern of mistakes
Finally, we expect a frequency of mistakes, roughly correlated with the concentration of activity, in a similar pattern observed in the history of intelligence (i.e. many minor mistakes, a few moderate, some major, and very rare catastrophic).
Detection
Most detections would be due to ETI mistakes
The vast majority of all detections would be due to mistakes on the part of ETI because of the extreme capabilities asymmetry between humanity and ETI.
Most ETI detections would be marginal
As a result, because most mistakes are minor, the majority of ETI detections are likely to be marginal and unclear. Because of the arms race nature of intelligence, we would expect this marginal pattern to remain even in the face of non-secret, widespread detector upgrades (e.g. the rise of widespread use of telescopes, cameras, etc.), as ETI would typically be tracking this capability and have updated their stealth approach and appetite for risk accordingly. Also, we would expect most detections to occur at night, or in other poor visibility times and locations, as this is likely when most covert intelligence is conducted, to minimise the chance of detection.
Very rare, clear detections, even by laypeople, would be expected
However, due to the presence of rare catastrophic mistakes, we would expect some rare instances where clear detection of ETI was possible, even by laypeople, resulting in non-reproducible eyewitness accounts from individuals or groups, spanning the whole of recorded history, across cultures and geographies. Most of these clear cases would likely to be detected by the military, due to their location near sensitive material and more advanced detector capabilities. Some clear accidental detections would also be expected by civilian experts (e.g. scientists, researchers).
As with the history of intelligence, we would expect some of these catastrophic mistakes to be technical failures (e.g. malfunction, loss of stealth, etc.) some to be unexpected interactions or incorrect assumptions (e.g. not expecting people to be present, underestimation of detector capability, etc.) and some might be misalignment of intentions (e.g. leaks or defectors, such as an individual ETI breaking stealth for ideological reasons, or potentially if one ETI group were attacked by another during an operation).
Eventually, a trend of tit-for-tat detections would arise
At some point of humanity’s technological development, detector capability would approach the minimum level of detection for ETI stealth. If such upgrades were kept secret from ETI (more likely with military technology), we would expect to begin to see a tit-for-tat arms race pattern of ETI detections. The result would be a rash of ETI detections immediately after deployment of secretly upgraded, global state of the art detector capabilities (most likely military, given that it would need to be secret), that quickly tail off as ETI become aware and upgrade their stealth tactics. This would then be expected to repeat each time a new secret upgrade to the global level of detector capabilities was deployed. (Note: This would be expected to only happen after the global leader in detection capabilities was upgraded, not every country independently.)
The overall pattern would be an initial, probably long period where humanity’s detection capabilities are below the detection level for ETI stealth (hence only infrequent detections from ETI mistakes), eventually overlaid with a tit-for-tat pattern of temporary periods of frequent detections (Figure 3). Obviously it is hard to guess when such a tit-for-tat pattern would emerge, because it depends on the stealth capability of ETI. But if there were multiple groups of clandestine ETI, then this would occur when we reached the detection level of the most unsophisticated group. The greater the number of ETI groups, the sooner this would likely be.
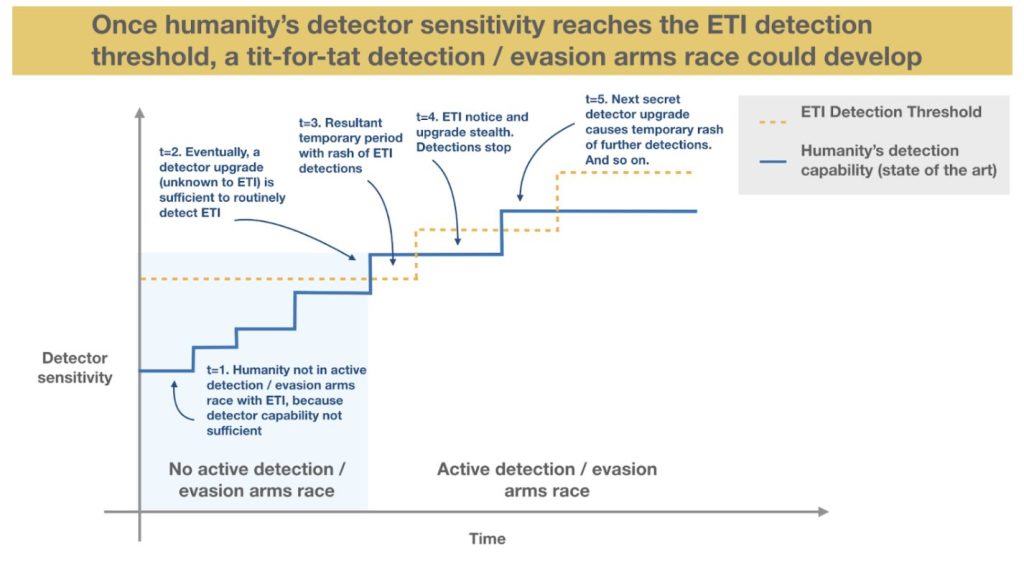
Figure 3. Once humanity’s detector sensitivity reaches ETI’s detection threshold, a tit-for-tat deception / evasion arms race could develop. Initially humanity’s detector capability is too low for upgrades to cause ETI detections (blue area). Eventually, secret upgrades of detector sensitivity rise beyond ETI’s stealth, and a rash of ETI detections are recorded until ETI upgrade their stealth.
Identification
General patterns of identification
Most ETI detections would be marginal, and will go unidentified
Because most detections would be marginal and unclear, most would go unidentified – either left unexplained, or assigned to out-of-the-ordinary terrestrial phenomena, such as military tests, rare weather events, etc. This is especially true for laypeople, because it is unlikely they would possess the contextual information or analysis techniques necessary for analysis.
Rare catastrophic mistakes by ETI would likely be unambiguously identifiable as ETI
However, due to the ETI’s extremely advanced technical capabilities and likely alien nature, at some threshold of detection clarity, it seems reasonable to expect that even laypeople would be able to fairly accurately identify ETI. Such events would probably require a catastrophic mistake on the part of ETI, and so would likely be extremely rare and non-reproducible –but some such cases would be expected.
Even clear ETI detections would mostly be ignored, or explained as terrestrial technology
Due to the likely non-reproducible nature of the evidence, and the extreme divergence from the prevailing worldview, when individuals in the military or laypeople reported such unambiguous detections, they would mostly be ignored by military or intelligence agencies because the implications are too far from what is considered possible, and the evidence too ephemeral (and especially by the scientific community, because the data is likely to be non-reproducible). Even if intelligence experts did take the detection reports seriously (e.g. if they came from military sources with detailed data) there would still the confounding factor that the evidence might be wrongly identified as advanced terrestrial technology (e.g. of foreign nations, or even secret domestic military technology) – despite the fact that in reality, some such cases would actually have been covert ETI.
Identification by the military
The military would likely be the first major group to become aware of ETI, but would be incentivised to keep it secret
Military and intelligence agencies would experience many more detections, and much higher clarity detections than other groups, and so would in some cases be expected to gradually build up a weight of evidence and a background of relevant contextual information (assuming data was centralised). Military and intelligence agencies would also likely be able to apply appropriate intelligence analysis methods to help with with identification. At some point (perhaps when detector technology increased sufficiently to start tit-for-tat rashes of detections), the military would have enough clear evidence to be accurately identify ETI. However, in such cases, there would be many risks with sharing this information. For example, there would be the risk that despite the clarity of the evidence, the detections were not ETI, but instead an advance of a terrestrial opponent, and going public might tip them off. Or if a military had indisputable evidence of ETI, there would also be the potential strategic risk of tipping off other terrestrial opponents about ETI. Finally, there would also be the risk of tipping off ETI themselves that the military was aware of them. (Given ETI’s extreme level of technical advancement and attempts to remain concealed, openly letting them know we were aware of them could be extremely risky.) Due to these risks, it seems likely any such information would be kept secret.
Identification by scientists
Due to methodological issues unfamiliarity with intentionally deceptive data, the scientific method would typically return false negatives regarding covert ETI, and hence the scientific community would be one of the last groups to become aware.
As discussed, the scientific method will routinely return type 2 errors (false negatives) when unwittingly used to assess subjects who are intentionally trying to deceive the investigator (Figure 2). Given that covert ETI would by definition be carrying out such deception, it seems likely that when studying data caused by covert ETI, the scientific method would commonly return false negatives. (And given that such deceptive data would likely be intentionally designed to reinforce the negative case, these erroneous results would perhaps come with a high degree of confidence).
This would be accentuated by the fact that we know nothing about ETI. As a result, there would be nothing to flag to scientists that ETI were likely to be deceptive, and hence were a phenomenon that would not normally be tackled with the strict scientific method, and that doing so may run a significant risk of systematic error. In addition, because science rarely studies such intentionally deceptive phenomena (especially fields most associated with ETI, such as astronomy, astrobiology, etc.), it is also unlikely that the scientists involved would be used to considering the possibility of deception or conspiracy, or be aware of the risks of using of the scientific method in such cases.
Rarely, some scientists would clearly detect ETI, but such events would be unlikely to be made public
In general, scientists would be no more likely to detect ETI than laypeople (i.e. rare occurrences, and mostly marginal, unclear detections due to ETI mistakes) because they are not commonly searching for covert intelligence, are not commonly in places where it is concentrated, and are unlikely to be using specialist intelligence methods for analysis or identification (etc.). (An exception to this would be scientists who work in military intelligence, but they would likely follow the military pattern described above due to being bound to secrecy).
But in some rare cases, we would expect non-military scientists working at the state of the art to accidentally detected ETI. And, due to the advanced nature of the detection equipment, such detections may be clear. However, detections would in some cases appear similar to advanced military technology, in which case they are likely to be reported to domestic intelligence agencies, who would typical opt to keep them secret. Even if they were not reported to intelligence agencies, the non-reproducible nature evidence (because ETI would likely be aware of detection and change their behaviour) and conspiratorial implications would likely act as a strong deterrent for scientists to publicly announce such results.
Due largely to these methodological issues, our analysis suggests that of all people, scientists may be some of the least likely to know, and least qualified to asses, if ETI were indeed spying on us.
Summary
In summary, if covert ETI were spying on humanity, we find that there would likely be some rare detectable evidence, initially caused by intermittent ETI mistakes, probably occurring at a very low but consistent frequency throughout human history. Practically all of this evidence would be non-reproducible, in part due to the active efforts of ETI monitoring the evolution of our detection capabilities and learning from their mistakes to remain hidden. The non-reproducible, intentionally deceptive nature of evidence would render the scientific method largely ineffective due to the high likelihood of type 2 statistical errors – consistently returning false negatives about the existence of ETI.
ETI spying would likely follow two trends: First, a consistent, long term, low frequency pattern of early-warning type intelligence collection, distributed diffusely across the globe (although generally away from populated areas) and stable through time; Second, a more recent trend of strategically focussed spying, concentrated on emerging, strategically sensitive targets that have potential for global impact (e.g. radiological and nuclear weapons, repositories of high-impact political, military or environmental strategy or capabilities), that would be expected to have increased significantly in parallel with humanity’s technological development and scope for global action.
Detections would likely follow a consistently marginal pattern, even in the face of ongoing improvements in our detection capabilities, as ETI remained one step ahead in the detection / evasion arms race. But eventually, once humanity’s detector capabilities approached the threshold of ETI stealth, a tit-for-tat pattern would emerge, where temporary rashes of ETI detections would immediately follow from a secret upgrade in global state of the art detection capabilities, only to quickly tail off as ETI realised and upgraded their stealth tactics accordingly.
Finally, our analysis suggests that some extremely rare events caused by catastrophic ETI mistakes would result in unambiguous identification of ETI, even by laypeople, which would result in extremely sparse clusters of ETI awareness, but that the non-reproducible nature of detections and extreme divergence from the currently accepted worldview would likely mean such identifications remained sparse, and would not typically be sufficient to convince any major groups. Due to their advanced detection and analysis capabilities, military and intelligence agencies would likely be the first major groups to become indisputably aware of ETI, followed by laypeople, and lastly perhaps the scientific community in general, due to science’s unfamiliarity with and aversion to conspiracy and deception, and the resulting methodological issues.
4. Discussion
From our analysis, we find it as a minimum plausible that advanced ETI would typically opt to remain hidden from, and actively spy on, human level civilisations, for universal, strategic intelligence reasons.
We also find that if ETI were spying on humanity, it is plausible that we would in some rare cases have detected and correctly identified ETI – but that due to the sparse and non-reproducible nature of the evidence, and systematic methodological issues, it is plausible that neither the public, nor the scientific community, would be aware of ETI.
In short, although we consider it unlikely, we find that it is to some degree plausible that covert ETI are currently spying on Earth, and that a scientific dismissal of the possibility out of hand may be too hasty.
Implications
The Great Game
The possibility that ETI might routinely spy and remain hidden from other civilisations raises the possibility that this is the default behaviour across the cosmos: That there is a galactic “great game” afoot, where practically all ETI groups routinely spy on, and remain hidden from, each other for strategic benefit.
But given the length of time some of these civilisations may have persisted, much of the strategically valuable information might eventually become common knowledge amongst older civilisations. At this point, the incentive for total secrecy would be lessen, perhaps enough to be overcome by benefit of trade and open cooperation amongst such groups.
In this scenario, any relics of older alien civilisations would also be hidden by current ETI groups, due to the risk of strategic loss if discovered, which could also help to explain why we have not detected any.
Overall, this hypothesis presents a solution the Fermi Paradox the preserves the copernican principle and broadly fits with terrestrial observations of nation-nation interactions.
Our analysis implies the possibility of clandestine ETI is perhaps not as unlikely as previously thought, and may warrant further investigation. Practically all current scientific research searching for ETI is based on the assumption that ETI will be passive about us detecting them. If clandestine ETI are in fact plausible, it may be worth investing in researching this possibility alongside existing efforts.
This analysis provides a simple answer for the Fermi Paradox that preserves the Copernican Principle, does not seem to require any obvious astronomically unlikely coincidences, and fits with common observations of interaction behaviour between terrestrial civilisations.
Testing
How could these predictions be tested? Given the arms race nature of covert intelligence, simply using the typical scientific method is likely to suffer from systematic errors and hence result in unreliable tests. (For example, when trying to detect a covert subject, if the experiments, detection methods and detector sensitivity were public knowledge before the experiments were carried out, then it is reasonable to assume that any covert subject may be aware in advance of our efforts to detect them, and counteract those efforts). Similarly, if we were to naively apply common heuristic rules to our tests, such as dismissing conspiracy, ignoring outliers, or expecting reproducible results, then they would also be likely to fail due to systematic errors.
Therefore, any reliable test would need a significantly modified version of the scientific method (that probably borrowed significantly from intelligence analysis methods). For example, a good starting point would be to keep all details of experiments, methods and detectors secret before the experiments were carried out; ensure that detector capabilities were at or beyond the current state of the art; expect deceptive behaviour (and so, for example, pay close attention to initial data / outliers, and expect a pattern of detections to stop once stealth was upgraded); look in places, and at times where covert intelligence is likely (e.g. near sensitive information, at times of low visibility), etc.
Although such research might still be relatively inexpensive compared to some existing research looking for ETI, this approach is a significant departure for science, and would likely be complicated and costly. Fortunately, military and intelligence agencies already have such capabilities and methods – therefore, a cheaper alternative may be to wait for evidence military or intelligence material declassified in the future, and compare the evidence to our predictions. The difficulty with this approach is that any such agencies may well be incentivised to keep exactly such evidence secret, and so there may be a long wait. Ultimately, what seems to be needed is a research program with the goals of science (understand the universe) but with the methodologies of intelligence. At present such tools and methods lie predominantly with intelligence agencies, whose goals instead centre on capturing strategic benefit and avoiding strategic risk (i.e. national security). While a hybrid approach is not difficult to imagine, it is hard to see how such differing goals could be reconciled.
Finally, we must consider that any successful scientific test (i.e. that discovered covert ETI and announced it publicly) would not be without risk – in particular, the risk that any such ETI must be highly advanced, and may not welcome being publicly disclosed.
Issues and limitations
Spying does not necessarily imply hostility
It is important to note that although covert intelligence is inherently adversarial on a basic level, this does not imply that any such covert ETI must always be inherently combative or hostile. Cooperation is often observed in covert intelligence situations. For example, during the India Pakistan nuclear crisis of 2002, the UK likely used their covert intelligence assets in both countries (present even though the UK are allies to both), helping to diffuse a crisis that would have been negative for all parties involved – instead facilitating a mutually beneficial solution. It is possible to imagine that covert ETI might remain covert for such mutually beneficial reasons [23].
Do they need to be here locally?
An important question is whether ETI would need to be in the close vicinity of earth to collect and usefully act on covert intelligence. If ETI are “spying” on us, but are at closest 500 lightyears away and cannot travel here in less than that time, then the analysis presented here falls down. It is extremely difficult to speculate on the spying capabilities of ETI. They could perhaps have capabilities that allow them to collect and act on all intelligence passively, without physical presence inside the solar system – in which case we would be extremely unlikely to detect them.
However, there are a number of reasons to consider that ETI, should they want to spy on us for strategic intelligence reasons, would be in the local vicinity. First, there may be fundamental or practical limitations that limit the distance from which information can be passively accessed, especially if the record of that information is small (e.g. in someone’s head) or highly protracted (e.g. underground, in a bunker). This is reflected in terrestrial intelligence: Practically all countries have physical intelligence assets (people, machinery, etc.) permanently stationed in other countries [22]. Second, some types of intelligence require physical co-location, such as physical sampling. Such methods may still be important, even with highly advanced passive remote sensing capabilities. And third, if we assume at least some ETI operate on similar timeframes to us, or care about things we do in that timeframe (e.g. we could realistically wipe out a significant proportion of life on earth in a few months with nuclear war), then such information is partly useful because it allows you to act to change events if need be – which would seem to require any such ETI to be within reasonable striking distance.
How can we tell ETI from terrestrial spying?
Another important question is how we can reliably tell clandestine ETI activity apart from terrestrial spying. This is difficult, because both would probably present as stealthy, out of the ordinary phenomena with advanced technology that is not publicly available. However, there are likely to be some differences. If we look at the history of spying, we see that advanced intelligence technology is sometimes a number of years, or even a few decades two ahead of the public state of the art [17], [40]. However, ETI technology would likely be thousands or millions of years ahead. Technology generally follows evolutionary patterns, in that later breakthroughs always build on and recombine earlier inventions. Saltationary advances are rare, and at significant magnitude are impossibly unlikely (e.g. jumping from the wheel to an iphone) [43]. Therefore, extremely advanced capabilities that far exceed both state of the art engineering and potentially our understanding of science, and that seem to sit far outside this terrestrial history of technology (e.g. that make dozens of saltationary technological leaps at once) would be a strong marker, this is essentially unprecedented in the history of technology or biological evolution. Evidence of alien biology that is clearly outside the evolutionary history of life on earth would be a clear marker for similar reasons. Such evidence is expected to be hard to come by, but may be available from catastrophic mistakes.
Limitations
The analysis we present here is speculative, but is constrained by existing frameworks (e.g. game theory, arms race dynamics and patterns of terrestrial covert intelligence). It is important to avoid unrestricted speculation.
Despite being informed by existing frameworks and data, the model is a crude first attempt, and would benefit from more detailed analysis. In particular, the model is based on a number of assumptions that are unknown (e.g. that intelligent life is common in the galaxy, often persists long enough to develop advanced technology, produces rational decision makers etc.). Furthermore, in absence of a sophisticated, quantitative and accepted model for expected behaviours in covert intelligence, we rely on basic game theory, and qualitative assumptions supported by the history of intelligence. Our research into the intelligence literature has been limited, in part due to our finite resources, and also by the sparse, likely biased nature of the available information. A more rigorous, quantitative and detailed analysis would be helpful.
5. Conclusions
Not long after the start of recorded history, Sun Tsu wrote the Art of War. Two and a half thousand years later, his treatise on intelligence is still one of the world’s most widely read strategic texts. Spying, it seems, is eternal. Despite the fact that it is foreign territory for science, covert intelligence is more widespread today than at any point in history: practically every country spies on every other, and spend millions (or even billions) doing it. Considering this, and the fact that spying is incentivised by extremely simple and common game theoretical conditions, it seems reasonable to wonder whether it is also a staple of the advanced ETI that Fermi Paradox suggests should be abundant in our galaxy, and could perhaps explain why we are yet to detect them.
Perhaps unusually, given the topic of this paper, we are not entirely convinced that covert ETI are spying on us. However, our analysis shows that as opposed to being an entirely crackpot idea that deserves prejudiced dismissal without testing, the possibility of covert ETI is a minimum plausible, finds support from game theory and the history of intelligence, and may warrant further scientific investigation. We expect this will be difficult, in part because questions where conspiracy is a sensible possibility almost always fall outside of science’s remit, and also because of the (in most cases very sensible) heuristic aversion to considering conspiracy as a realistic option in the scientific method.
Although these rules are heuristics, given how rare exceptions are, it is easy to understand why they might instead become dogma. But large scale conspiracies undeniably exist – as any veteran of Pearl Harbour or D-Day can attest. If our scientific method is hammer, that does not mean everything we want to understand must be a nail.
“… most of the time, as with the weather, forecasting that tomorrow will be like yesterday, but more so with the current trend extrapolated, will enhance your reputation for prediction. But you will, on a small but significant number of occasions, be wrong, and when you are wrong you may be spectacularly wrong. Intelligence agencies will say truthfully to their customers that ‘there is no evidence’ … but absence of evidence is not evidence of absence. Should the evidence appear, then the intelligence judgment will change instantly, as the equivalent of the black swan is observed.”
–David Omand
6. Bibliography
[1] S. Tzu, The art of war. Routledge, 2008.
[2] J. D. Haqq-Misra and S. D. Baum, ‘The sustainability solution to the Fermi paradox’, arXiv preprint arXiv:0906.0568, 2009.
[3] S. Webb, If the universe is teeming with aliens… where is everybody?: seventy-five solutions to the fermi paradox and the problem of extraterrestrial life. Springer, 2015.
[4] S. Bryson et al., ‘The Occurrence of Rocky Habitable-zone Planets around Solar-like Stars from Kepler Data’, The Astronomical Journal, vol. 161, no. 1, p. 36, 2020.
[5] D. Clery, ‘How big money is powering a massive hunt for alien intelligence’, Science | AAAS, Sep. 10, 2020. https://www.sciencemag.org/news/2020/09/how-big-money-powering-massive-hunt-alien-intelligence (accessed Jun. 22, 2021).
[6] R. Hanson, ‘The Great Filter-Are We Almost Past It?’, preprint available at http://hanson. gmu. edu/greatfilter. html, 1998.
[7] P. D. Ward and D. Brownlee, Eds., ‘Mass Extinctions and the Rare Earth Hypothesis’, in Rare Earth: Why Complex Life is Uncommon in the Universe, New York, NY: Springer, 2000, pp. 157–189. doi: 10.1007/0-387-21848-3_8.
[8] L. K. Scheffer, ‘Machine Intelligence, the Cost of Interstellar Travel and Fermi’s Paradox’, Quarterly Journal of the Royal Astronomical Society, vol. 35, p. 157, 1994.
[9] J. A. Ball, ‘The zoo hypothesis’, Icarus, vol. 19, no. 3, pp. 347–349, 1973.
[10] S. Baxter, ‘The planetarium hypothesis-a resolution of the Fermi paradox’, Journal of the British Interplanetary Society, vol. 54, pp. 210–216, 2001.
[11] C. Liu, The dark forest, vol. 2. Macmillan, 2015.
[12] ‘Aliens, The Fermi Paradox, And The Dark Forest Theory’, Project Nash, Oct. 12, 2020. https://www.projectnash.com/aliens-the-fermi-paradox-and-the-dark-forest-theory/ (accessed Jun. 22, 2021).
[13] M. Ross, ‘A brief history of SETI’, in The Search for Extraterrestrials: Intercepting Alien Signals, M. Ross, Ed. New York, NY: Praxis, 2009, pp. 95–97. doi: 10.1007/978-0-387-74070-6_10.
[14] ‘2020 Activity Report of the SETI Institute’. Accessed: Jun. 22, 2021. [Online]. Available: https://www.seti.org/2020-activity-report-seti-institute
[15] E. Solan and L. Yariv, ‘Games with espionage’, Games and Economic Behavior, vol. 47, no. 1, pp. 172–199, 2004.
[16] M. Maschler, E. Solan, and S. Zamir, ‘Game theory (translated from the hebrew by ziv hellman and edited by mike borns)’, Cambridge University Press, Cambridge, pp. xxvi, vol. 979, p. 4, 2013.
[17] P. Wright, P. Greengrass, and G. Ladjadj-Koenig, Spycatcher. Heinemann Melbourne, 1987.
[18] C. Andrew, The Defence of the Realm: The Authorized History of MI5. London: Penguin, 2010.
[19] R. Dawkins and J. R. Krebs, ‘Arms races between and within species’, Proceedings of the Royal Society of London. Series B. Biological Sciences, vol. 205, no. 1161, pp. 489–511, 1979.
[20] P. Zu et al., ‘Information arms race explains plant-herbivore chemical communication in ecological communities’, Science, vol. 368, no. 6497, pp. 1377–1381, 2020.
[21] R. P. Smith, ‘The influence of the Richardson arms race model’, Lewis Fry Richardson: His Intellectual Legacy and Influence in the Social Sciences, p. 25, 2020.
[22] C. Andrew, The secret world: a history of intelligence. Penguin UK, 2018.
[23] D. Omand, Securing the state. Oxford University Press, 2014.
[24] S. Kent, ‘The need for an intelligence literature’, Studies in Intelligence, vol. 1, no. 1, pp. 1–11, 1955.
[25] K. Popper, The logic of scientific discovery. Routledge, 2005.
[26] K. R. Popper, The open society and its enemies, vol. 119. Princeton University Press, 2020.
[27] W. Laqueur, A world of secrets: The uses and limits of intelligence. Basic Books New York, 1985.
[28] M. Warner, ‘Wanted: A definition of intelligence’, CIA Center for the Study of Intelligence, 2002.
[29] J. Hughes-Wilson, The Secret State. Simon and Schuster, 2017.
[30] D. C. Logan, ‘Known knowns, known unknowns, unknown unknowns and the propagation of scientific enquiry’, Journal of Experimental Botany, vol. 60, no. 3, pp. 712–714, Mar. 2009, doi: 10.1093/jxb/erp043.
[31] D. M. Kreps, P. Milgrom, J. Roberts, and R. Wilson, ‘Rational cooperation in the finitely repeated prisoners’ dilemma’, Journal of Economic theory, vol. 27, no. 2, pp. 245–252, 1982.
[32] R. Axelrod and W. D. Hamilton, ‘The evolution of cooperation’, science, vol. 211, no. 4489, pp. 1390–1396, 1981.
[33] B. Hillier, The economics of asymmetric information. Macmillan International Higher Education, 1997.
[34] J. G. White, E. Southgate, J. N. Thomson, and S. Brenner, ‘The structure of the nervous system of the nematode Caenorhabditis elegans’, Philosophical Transactions of the Royal Society of London. B, Biological Sciences, vol. 314, no. 1165, pp. 1–340, Nov. 1986, doi: 10.1098/rstb.1986.0056.
[35] ‘Bounded rationality in C. elegans is explained by circuit-specific normalization in chemosensory pathways | Nature Communications’. https://www.nature.com/articles/s41467-019-11715-7 (accessed Jun. 23, 2021).
[36] J. R. Stevens, ‘Rational decision making in primates: The bounded and the ecological’, in Primate neuroethology, New York, NY, US: Oxford University Press, 2010, pp. 98–116. doi: 10.1093/acprof:oso/9780195326598.003.0006.
[37] M. M. Waldrop, ‘Space Reactors Hinder Gamma-Ray Astronomy: Soviet nuclear spy satellites are hurting gamma-ray astronomy; so why was that fact classified for 8 years?’, Science, vol. 242, no. 4882, pp. 1119–1120, Nov. 1988, doi: 10.1126/science.242.4882.1119.
[38] F. G. Powers and C. Gentry, Operation Overflight: A Memoir of the U-2 Incident. Potomac Books, Inc., 2004.
[39] J. Donovan, Strangers on a Bridge: The Case of Colonel Abel and Francis Gary Powers. Simon and Schuster, 2015.
[40] E. Snowden, Permanent record. Pan Macmillan, 2019.
[41] M. K. Dhami, I. K. Belton, and D. R. Mandel, ‘The “analysis of competing hypotheses” in intelligence analysis’, Applied Cognitive Psychology, vol. 33, no. 6, pp. 1080–1090, 2019.
[42] D. M. Hawkins, Identification of outliers, vol. 11. Springer, 1980.
[43] G. Basalla, The Evolution of Technology. Cambridge University Press, 1988.
